SSL errors are never a pretty sight. You may encounter one in the most unexpected places, as no one is “immune” from them, even powerhouses such as Microsoft. This week, Mozilla Firefox web browser users could not access Microsoft.com and its subdomains. Reports worldwide indicated that the error stemmed from Firefox itself, as all Microsoft websites were accessible via Chrome and other browsers.
A quick glance at the error log and the accompanying message revealed the culprit:
‘MOZILLA_PKIX_ERROR_OCSP_RESPONSE_FOR_CERT_MISSING’ and the message “The OCSP response does not include a status for the certificate being verified,” help trace down the cause of the issue.
OCSP stands for Online Certificate Status Protocol, a method for browsers to determine the validity of an SSL certificate instead of relying on traditional revocation lits. However, the original OCSP has a few shortcomings, which are improved by a feature called OCSP Stapling.
With OCSP stapling the web server queries the CA on the status of the SSL certificate, and the CA delivers a highly secure digitally time-stamped response. Now, when the webserver connects to a browser, it binds the signed time-stamp with the SSL certificate, making the verification quicker. Instead of reaching the CA, the browser verifies the server’s time stamp, and since it’s from a reliable CA, trusts the Certificate.
OCSP stapling is enabled by default in Firefox since 2013. Here’s what Mozilla’s Dana Keeler thoughts were on how OCSP stapling improves the OCSP protocol:
OCSP stapling solves these problems by having the site itself periodically ask the CA for a signed assertion of status and sending that statement in the handshake at the beginning of new HTTPS connections. The browser takes that signed, stapled response, verifies it, and uses it to determine if the site’s certificate is still trustworthy. If not, it knows that something is wrong and it must terminate the connection. Otherwise, the certificate is fine and the user can connect to the site.
The OCSP stapling has been working as intended all these years, but it seems that a bug showed its presence 8 years after its introduction. So what triggered it?
What caused the OSCP stapling error?
Back in 2013, Firefox did not yet recognize the SHA-2 family of hashes, such as SHA-256, in the CertID fields that are present in OCSP responses it receives. As such, any certificate containing the SHA-256 hashes, as opposed to the older SHA-1, is considered invalid and causes Firefox to terminate the connection with the website.
How to fix the Firefox SSL error?
Until Mozilla solves this issue, you need to disable the OCSP stapling in Firefox to access Microsoft websites. Here’s how to do it:
- Type about:config in their address bar and hit Enter.
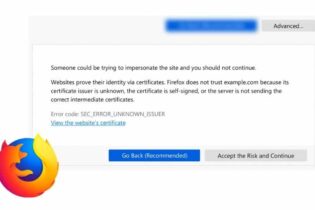
- Click the Accept the Risk and Continue button, following the Proceed with caution warning message.
- In the Search preference name text box, type “stapl”.
- The following two settings will show up:
security.ssl.enable_ocsp_must_staple true
security.ssl.enable_ocsp_stapling true - Double-click on each of these settings to switch these to false.
- The changes take immediate effect. You should now access the Microsoft website without a problem.
Firefox Update
As expected, Firefox swiftly fixed the error in the 95.01 release. Here’s what the release notes say:
Fixed frequent MOZILLA_PKIX_ERROR_OCSP_RESPONSE_FOR_CERT_MISSING error messages when trying to connect to various microsoft.com domains.
If you’ve encountered other SSL connection errors while browsing, and are looking for a quick fix, check our page dedicated to SSL errors. Our tutorials offer easy solutions to the common Chrome and Firefox issues.
Save 10% on SSL Certificates when ordering today!
Fast issuance, strong encryption, 99.99% browser trust, dedicated support, and 25-day money-back guarantee. Coupon code: SAVE10