Important Update!
Starting from June 1st, 2023, a new security measure is in place for code signing certificates. All code signing certificates must now be stored on hardware meeting specific security standards such as FIPS 140 Level 2, Common Criteria EAL 4+, or their equivalents.
As a result, the process of obtaining and installing certificates has changed. Certificate Authorities no longer support browser-based key generation, creating CSRs, and installing certificates on laptops or servers. Instead, if you opt for token + shipment as your code signing delivery method, the CA will handle CSR generation. Alternatively, if you prefer to use your Hardware Security Module (HSM), check the guides below or follow your HSM provider’s instructions for CSR generation.
- YubiKey 5 FIPS CSR Generation and Attestation
- Luna Network Attached HSM v7.x: CSR & Attestation Guide
The following text contains outdated information, no longer applicable to CSR generation for code signing certificates.
This guide explains how to generate a Certificate Signing Request on Mac when applying for a code signing certificate. The CSR is a block of encoded text with information about yourself and your company. It includes your first and last names, the company’s official name, country and city of residence, and a valid contact email.
How to Create a CSR on Mac
Follow the steps below to generate the CSR on Mac using the Keychain.
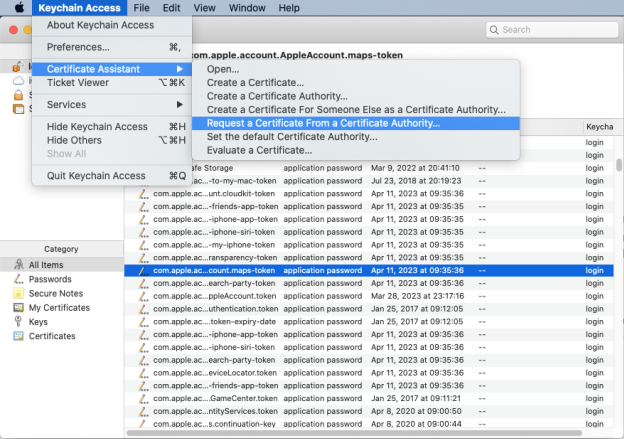
Step 1. Open Keychain and Request Your Certificate
Open “Keychain Access” and go to the “Certificate Assistant” menu.
Click on “Request a Certificate from a Certificate Authority”.
Step 2. Enter the Required Information
In the “Certificate Assistant” window, enter the required information such as the common name and email address.
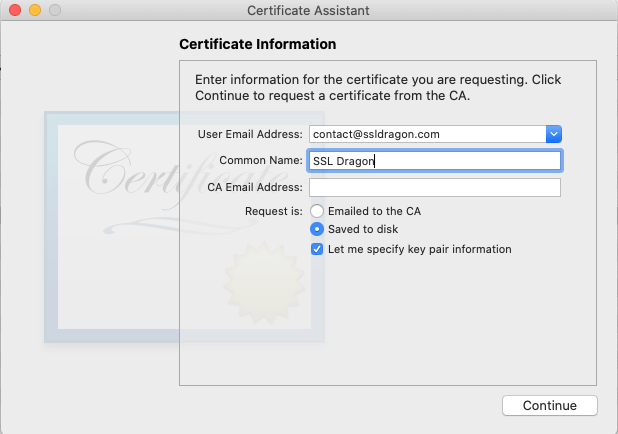
Note that for code signing certificates, the “Common Name” must be the name of the organization or individual requesting the certificate. For demonstration purposes, we’ve used SSL Dragon as the CN. Instead of inputting the “CA Email Address”, choose “Saved to Disk” to specify a location on your Mac where the CSR text file will be saved.
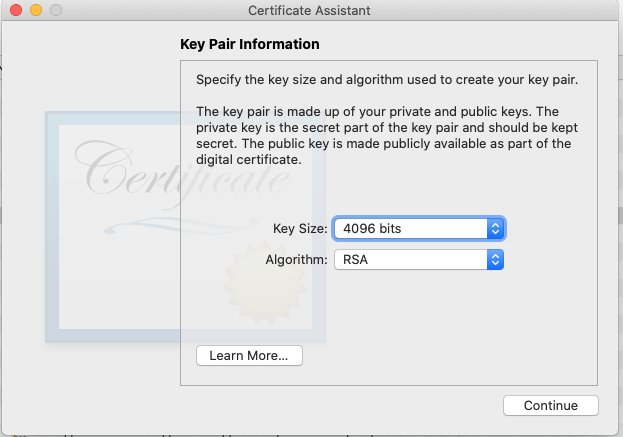
Step 3. Specify Key Pair Size
If you’re generating a code signing certificate or need a CSR greater than 2048 bits, select “Let me specify key pair information”. Otherwise, click “Continue”. Choose your preferred key size (code signing requires at least 3072 bits) and then click “Continue”.
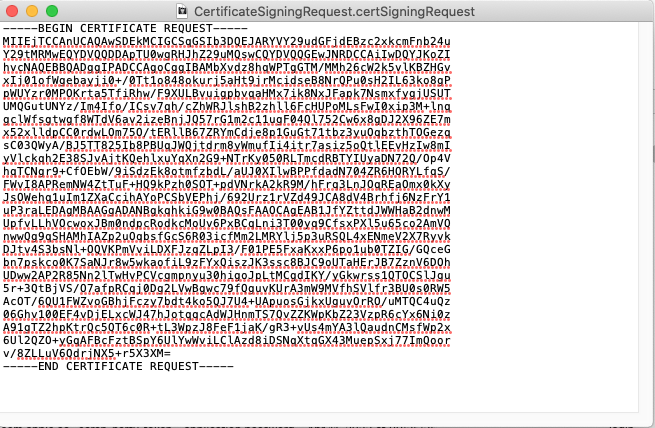
Step 4. Open Your Csr File and Copy-Past Its Contents During the Certificate Order
After saving the CSR file, open it in “TextEdit” by right-clicking on the file and selecting “Open With”.
Copy and paste all the text from the CSR file, including the “BEGIN CERTIFICATE REQUEST” and “END CERTIFICATE REQUEST” tags, into the CSR field on your account’s order generation form.
Once you’ve generated the CSR, the validation process will begin.
Locate the Private Key
If you’re wondering where the private key is, search for the CSR’s common name in the Login keychain under “All Items”. You should see a public key (the CSR) and a private key that matches the Common Name you entered when generating the CSR.
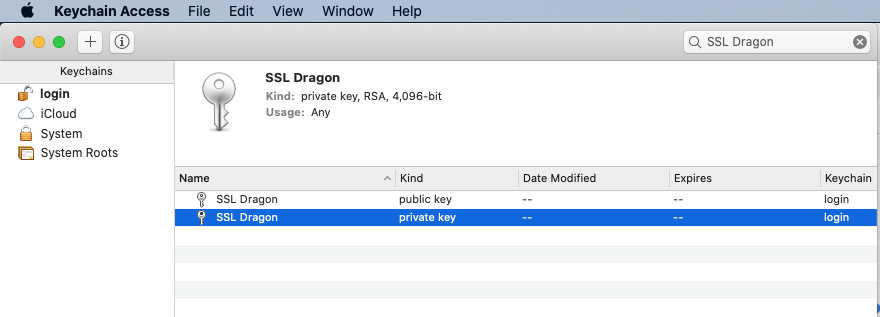
Keep your private key safe and never share or delete it, as you’ll need it during installation.
By following these steps, you can create a certificate signing request on Mac and obtain a valid certificate for your needs.
Final Steps
After you generate a Certificate Signing Request on Mac and submit it to the CA, it will check your identity and business credentials before delivering the certificate. It may take 1 to 3 business days to sign the code signing cert. Once you get the necessary files, you can install them on your system.
Save 10% on SSL Certificates when ordering today!
Fast issuance, strong encryption, 99.99% browser trust, dedicated support, and 25-day money-back guarantee. Coupon code: SAVE10