You’ve probably heard about brute force attacks, but might be wondering: what is a brute force attack exactly?
Imagine a thief trying every possible key to open a lock — that’s essentially what a brute force attack is, but in the digital world.
In this article, you’ll learn how they work, why they’re used, the different types, and most importantly, how you can prevent them.
Let’s dive into the murky waters of cyber threats.
Table of Contents
- What Is a Brute Force Attack?
- How Does a Brute Force Attack Work?
- The Reasons for Brute Force Attacks
- The Different Types of Brute Force Attacks
- How to Prevent Brute Force Attacks
What Is a Brute Force Attack?
In the simplest terms, a brute force attack is a trial-and-error method used by attackers to gain access to an account or system. Attackers use automated software to generate a large number of consecutive guesses to crack a password or data encryption.
Imagine you’re trying to crack a padlock with a three-digit code. You’d start with 000 and work your way up to 999, right? That’s a brute force attack example. It’s a blind and straightforward approach, but it can be effective, especially against weak passwords.
How Does a Brute Force Attack Work?
In understanding a brute force attack, you must grasp how it works, and it’s actually quite straightforward. A brute force attack works by using vast computing power to systematically try all possible passwords until the correct one is found. This is done by making a repeated login attempt until the correct password is locked in.
Brute force attacks can be time-consuming and require a lot of computational resources. That’s why they’re often used as a last resort when other, more sophisticated hacking methods fail.
Now, let’s dig a bit deeper. Imagine you’ve got a combination lock and you’ve forgotten the code. You’re left with no choice but to try every possible combination until you hit the right one. That’s essentially how a brute force attack works. However, in the realm of cybersecurity, the lock is a user account, and the combinations are possible passwords.
The key to a successful brute force attack is persistence and enough computing power. The more complex the password, the more password combinations there are to try. It’s a simple, yet effective method of hacking, and one that can be devastating if you’re not adequately protected.
The Reasons for Brute Force Attacks
You might be wondering why brute force attacks happen in the first place.
The motivations behind these attacks can range from financial gain to the desire to spread chaos.
Let’s look at some common reasons why an attacker might resort to this method.
1. Exploiting Ads and User Data
One reason you’d conduct a brute force attack is to exploit ads or user data for financial gain. Hackers often use this method to steal data, particularly user activity data. They crack passwords to access personal accounts and aim to exploit ads that are targeted based on your activity data. This often leads to significant financial profit for the cybercriminals.
Now, you might wonder how this works. These criminals sell your activity data to third-party companies. These companies then use this information to tailor ads specifically to your interests, which increases their chances of making a sale. In essence, a brute force attack can be a lucrative business for those without scruples.
2. Data Theft and Identity Fraud
Not only can brute force attacks lead to financial gain through ad exploitation, but they’re also frequently used to steal personal data for identity theft.
This method involves launching a brute force attack to gain unauthorized access to your account. The motive? To steal personal data for financial gain or identity theft.
By breaking down your password security, they can breach your data, obtaining sensitive information. These data breaches often result in stolen identities and financial loss.
They’ll use your credit card details, social security number, or other personal data to commit fraudulent activities.
3. Malware Propagation
In the world of cybercrime, brute force attacks aren’t just about stealing personal information, but they’re also about spreading malware to infect systems and launch wider attacks. With brute force hacking, cybercriminals can infiltrate your network and spread harmful software. This malware can infect systems, corrupting files and causing significant damage.
But why stop there? Once they’ve compromised one system, they can use that as a launchpad to initiate wider attacks. They can potentially access and infect other interconnected systems, spreading the malware even further. The goal of this brute force attack isn’t just to cause havoc in one place, but to spread the destruction as far as possible.
4. System Hijacking for DDoS Actions
While you might think brute force attacks are solely about stealing data, they’re often used to hijack systems for malicious activities, such as DDoS attacks. By guessing a known password, a brute force attack can gain entry to your network.
Once inside, the attacker can take control, turning your system into a weapon to launch DDoS attacks on other networks. This malicious activity can cause massive disruption, often resulting in significant downtime and financial loss for the affected businesses.
It’s not just about getting unauthorized access, but also about using that access to cause widespread harm. So, it’s crucial to protect your digital assets from these potential threats.
5. Damaging Brands and Website Defacement
You might believe brute force attacks simply disrupt systems, but they also have the potential to ruin a company’s reputation by stealing data or defacing the website.
When an attacker uses a brute force attack to steal data, it’s not just about gaining unauthorized access. They’re after sensitive information, which they can use to their advantage or sell to the highest bidder.
With this stolen data, they can cause significant harm to a company’s reputation. Similarly, by defacing the site, the attacker can create a sense of insecurity among its users.
This can impact the website’s reputation, leading to loss of trust and potential business.
The Different Types of Brute Force Attacks
Now, let’s move on to understanding the different types of brute force attacks.
You may think it’s a one-size-fits-all method, but there are actually four main types:
- Simple brute force attacks
- Dictionary attacks
- Hybrid brute force attacks
- Reverse brute force attacks
Each type of brute force attack has its own unique traits and methods, which we’ll discuss next.
1. Simple Brute Force Attacks
A simple brute force attack involves systematically trying all possible combinations of characters until the correct one is found. It is the most basic and time-consuming method, but it can be effective for weak passwords.
This attack method doesn’t require much sophistication; it’s all about persistence.
In some cases, the attacker may attempt every single combination of letters, numbers, and symbols until they find the right one.
2. Dictionary Attacks
Instead of trying all possible combinations, a dictionary attack uses a pre-existing list of widely used passwords, known as a dictionary. It saves time by only testing a predefined set of options, making it more efficient than a simple brute force attack.
They depend on the fact that many people use simple, easily guessed passwords.
By using a list of the most common passwords, a dictionary attack can often swiftly bypass security. Therefore, you should always avoid simple, common password combinations.
3. Hybrid Brute Force Attacks
A hybrid brute force attack combines elements of both simple brute force and dictionary attacks. It starts with a dictionary list but then adds variations to each word, such as adding numbers or special characters. This method increases the chances of success by covering a wider range of possible passwords.
This method is more efficient than a regular brute force attack and more effective against complex passwords.
4. Reverse Brute Force Attacks
Unlike the previous types, a reverse brute force attack targets a specific user or multiple usernames instead of a single password. Instead of trying different passwords against a single account, it tries a single password against multiple accounts. It is a more targeted approach and can be useful when the attacker has some information about the target.
A key sign of a reverse brute force attack is a high number of failed login attempts from different user accounts but with the same password. So, always be vigilant with your account security. Don’t use common passwords and keep a close eye on failed login attempts.
How to Prevent Brute Force Attacks
You can prevent brute force attacks in a number of ways.
1. Use Stronger Password Practices
It’s crucial to create complex passwords that are hard for hackers to guess. Password complexity is your best friend in this situation.
Consider using a mix of uppercase and lowercase letters, numbers, and special characters to strengthen passwords. This makes it difficult for brute force attacks to crack your password.
Furthermore, password education plays a significant role in preventing these attacks. Understand the risks and learn how to protect yourself. Stay updated on the latest ways to secure your data.
2. Better Protect User Passwords
To better protect your passwords against brute force attacks, two primary methods should be employed:
- Always use unique passwords for each of your accounts.
- You should consider using a password manager to generate and store complex, unique passwords.
3. Two-factor Authentication
Consider using two-factor authentication whenever it’s available. It requires you to confirm your identity by providing two separate pieces of evidence. It significantly reduces the chances of a successful brute force attack, helping to better protect user passwords.
It’s not foolproof, but it can certainly stop a brute force attack in its tracks, boosting your cybersecurity significantly.
4. Captcha
By using CAPTCHA, you’re adding another layer of defense against brute force attacks. This tool helps prevent brute force attacks by requiring users to prove they’re not a computer before they can proceed. CAPTCHA often asks you to identify objects or characters in an image, a task that’s easy for humans but challenging for bots. When hackers attempt to use software to automate a login attempt, CAPTCHA will stop them in their tracks.
Each failed CAPTCHA attempt flags the user, protecting the target server from being overwhelmed. So, next time you grumble at the extra step, remember, it’s there to protect you. It’s an effective method to deter those persistent brute force attackers and keep your information secure.
5. Limit Login Attempts
You’ll significantly increase your protection against brute force attacks if you limit login attempts on your account. This measure deters attackers by reducing the chances of a successful exhaustive key search.
Remember, a brute force attack involves trying every possible password combination to gain unauthorized access. By restricting how many times someone can attempt to log in, you make this process exponentially more difficult.
This step is especially helpful against credential stuffing, where attackers use stolen passwords. If they can’t get in after a few attempts, they’re likely to move on.
6. Cloudflare
Cloudflare acts like a shield, protecting your encryption keys from rainbow table attacks, a type of brute force attack that uses precomputed tables to crack password hashes.
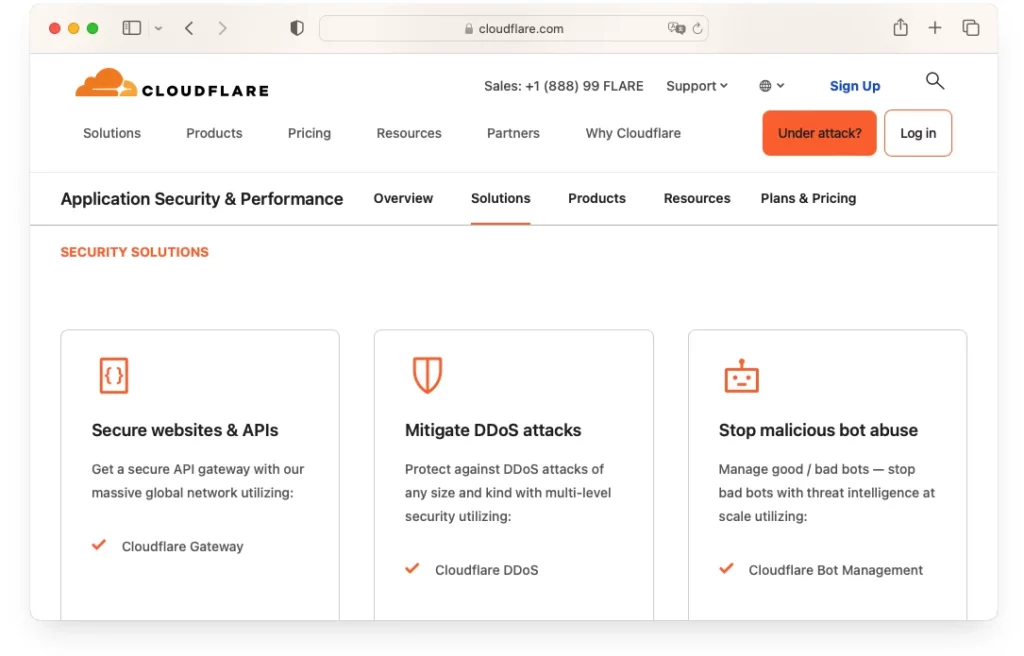
The service monitors traffic to your site, identifying and blocking suspicious activity. It’s a powerful tool in the fight against cyber threats, making it much harder for hackers to succeed.
Cloudflare might be your best bet if you’re serious about security.
FAQ
Are Brute Force Attacks Illegal?
Yes, brute force attacks are illegal as they involve unauthorized access to systems and data.
Is Brute Force a DDOS Attack?
No, while both are cyberattacks, they are different. Brute force targets passwords or encryption, while DDoS overwhelms a system with traffic.
How Long Can a Brute Force Take?
It varies widely based on password complexity and the attacker’s computational power. It can range from minutes to years.
Is a Birthday Attack a Brute Force Attack?
No, a birthday attack is a specific type of cryptographic attack that exploits the mathematics behind the birthday problem in probability theory.
Is Brute Force the Same as Password Cracking?
Yes, brute force is a method of password cracking. However, not all password cracking uses brute force; there are other methods too.
Conclusion
So, now you’ve learned what a brute force attack is, how it works, and why hackers use it.
You also understand the different types of brute force attacks and how to prevent them.
Remember, it’s crucial to stay vigilant and proactive in securing your data. Always keep your passwords complex and unique, and consider using tools that detect and prevent these attacks.
Stay safe in the digital world!
Save 10% on SSL Certificates when ordering today!
Fast issuance, strong encryption, 99.99% browser trust, dedicated support, and 25-day money-back guarantee. Coupon code: SAVE10